Unlocking the Digital Secret: What is a Cryptographic Hash Function?
In our digital world, we constantly need to verify the integrity and authenticity of information. Whether you’re downloading software, entering a password, or making a cryptocurrency transaction, a silent guardian works in the background to keep things secure. This guardian is called a cryptographic hash function.
Let’s break down what it is, how it works, and why it’s so fundamental to our online safety.
What is a Cryptographic Hash Function?
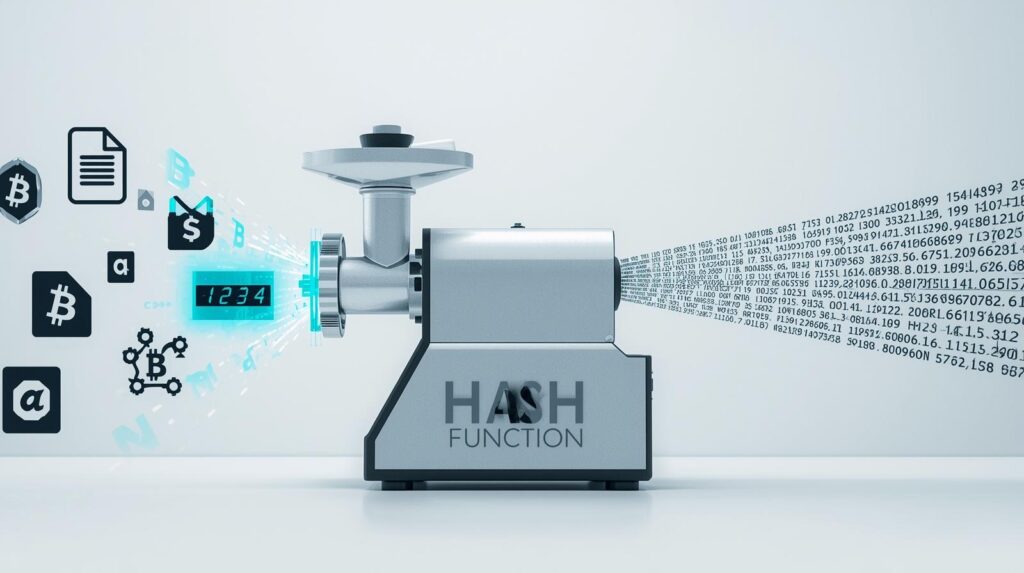
At its core, a cryptographic hash function is a special mathematical algorithm that takes any input (like a file, text, or password) and produces a fixed-size string of characters, which looks like a random jumble of letters and numbers. This output is called a hash value, digest, or most intuitively, a “digital fingerprint.”
Imagine it as a highly sophisticated digital meat grinder:
- You can put any food into it—a steak, a carrot, or even a three-course meal (the input).
- The grinder will always produce the same consistent, finely ground output (the hash).
- You cannot take the ground output and reconstruct the original steak (it’s one-way).
- If you change the input ever so slightly—like adding a single grain of salt—the output will be completely different.
The “Magic” Properties: What Makes it Cryptographic
Not all hash functions are cryptographic. What sets them apart is a set of specific, crucial properties:
- Deterministic: The same input will always produce the exact same hash value. Every. Single. Time.
- Fast to Compute: It’s very quick for a computer to calculate the hash from any given input.
- Pre-image Resistance (One-Way Function): This is the “you can’t get the steak back from the grind” property. If you only have a hash value, it should be computationally infeasible to figure out what the original input was.
- Avalanche Effect: A tiny, minuscule change in the input completely changes the output hash.
- Input:
Hello- Hash (SHA-256):
185f8db32271fe25f561a6fc938b2e264306ec304eda518007d1764826381969
- Hash (SHA-256):
- Input:
hello(just a capital ‘H’ changed to lowercase ‘h’)- Hash (SHA-256):
2cf24dba5fb0a30e26e83b2ac5b9e29e1b161e5c1fa7425e73043362938b9824
Notice how the two hashes are completely unrecognizable from each other? That’s the avalanche effect.
- Hash (SHA-256):
- Input:
- Collision Resistance: It should be extremely difficult to find two different inputs that produce the same hash output. In theory, collisions can exist because the input is infinite and the output is fixed in size, but finding them should be practically impossible.

How Does it Work? A Simplified Look Under the Hood
While the actual math is complex (involving bitwise operations, modular addition, and logical functions), we can understand the general process:
- Input Reception: The function takes your input data.
- Padding and Splitting: The input is padded to a specific length and then broken down into fixed-size blocks.
- Initialization: The algorithm starts with a default internal state (a pre-defined starting hash value).
- Compression Loop: Each block of data is mixed into the internal state using a special compression function. The output from processing the first block becomes part of the input for processing the second block, and so on. This creates a chain-like dependency.
- Finalization: After all blocks have been processed, the final internal state is the hash value that is output.
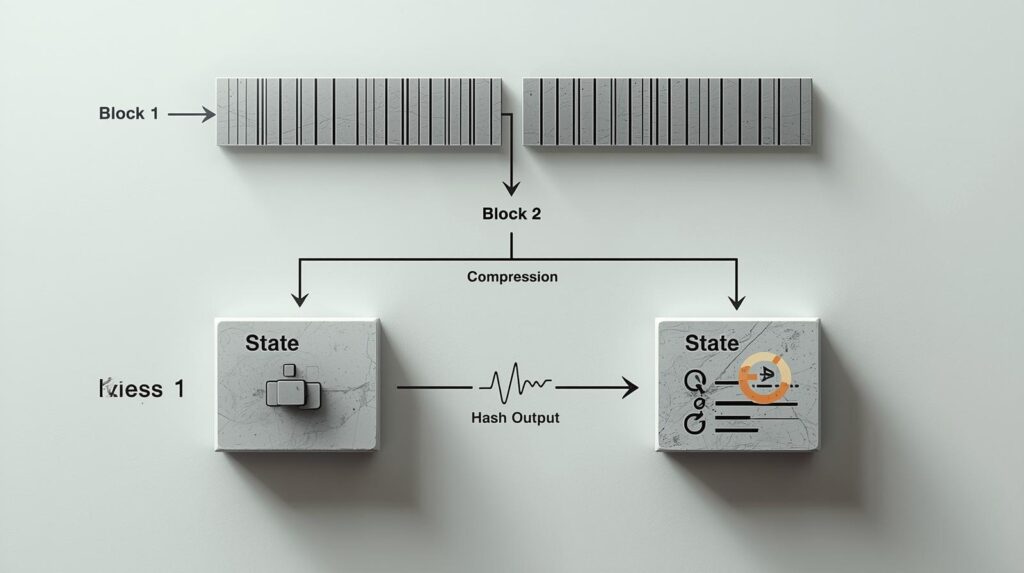
This chaining effect is why the avalanche effect works so well. A change in one early block cascades through all subsequent blocks, radically altering the final result.
Real-World Applications: Where You See Hashes in Action
Cryptographic hashes aren’t just theoretical; they are the workhorses of modern digital security.
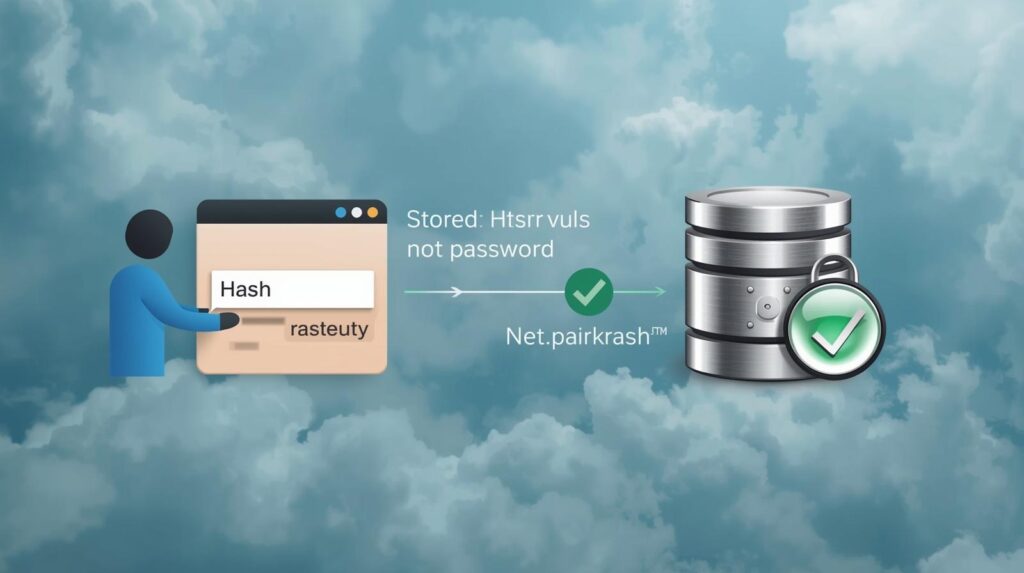
- Password Storage: When you create a password on a website, a good service doesn’t store your actual password. Instead, it stores its hash. When you log in, it hashes the password you type and compares it to the stored hash. If they match, you’re in! This means even if hackers breach the database, they don’t get your plaintext passwords. (Read more about How to Safely Store a Password)
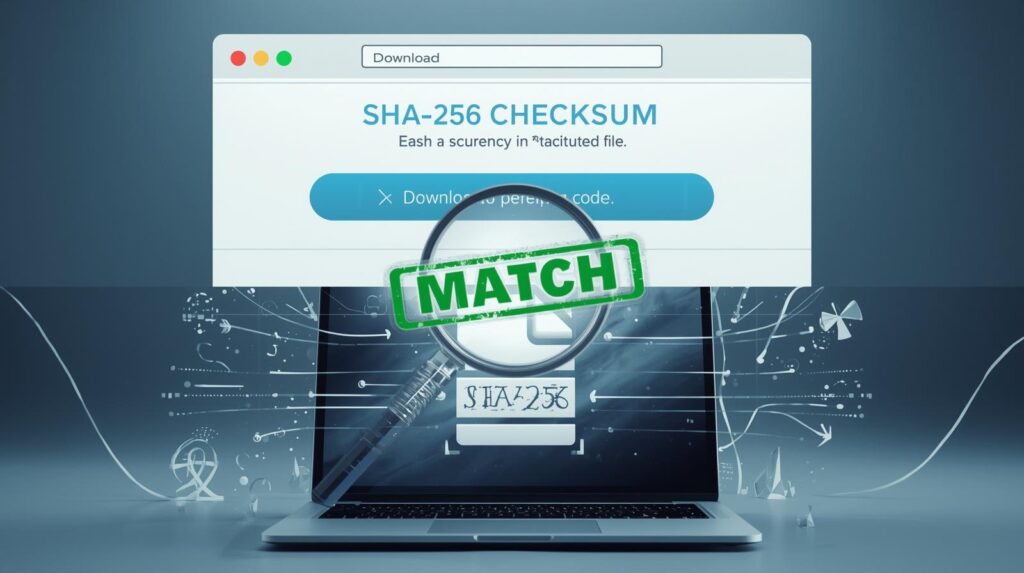
- Data Integrity Verification: When you download a large file (like an operating system or software), the website often provides a hash checksum. After downloading, you can generate a hash of your local file. If it matches the official one, you can be 100% sure the file wasn’t corrupted or tampered with during download.
- Digital Signatures and Certificates: In the SSL/TLS certificates that secure websites (the
https://ones in your address bar), hashes are used to create a unique signature that verifies the certificate’s authenticity, ensuring you’re connected to the real website and not an imposter. (Learn about How SSL Certificates Work) - Blockchain and Cryptocurrencies: Blockchains like Bitcoin rely heavily on hashing. Blocks of transactions are linked together using their hashes, creating a tamper-evident chain. If someone alters a past transaction, its hash changes, breaking the chain and alerting everyone to the foul play. (Explore the Bitcoin Whitepaper)
Common Hash Functions You Might Encounter
- MD5: Once popular, now considered broken and insecure due to vulnerability to collisions. Do not use for security purposes.
- SHA-1: Was a standard but has significant weaknesses and is now considered insecure.
- SHA-2 Family (e.g., SHA-256, SHA-512): This is the current gold standard and is widely used today (e.g., in Bitcoin, TLS certificates). (See the SHA-2 standard from NIST)
- SHA-3: The newest member of the Secure Hash Algorithm family, designed as a future-proof alternative to SHA-2.
Conclusion
A cryptographic hash function is a fundamental pillar of cybersecurity. By acting as a unique, one-way digital fingerprint, it allows us to verify data, secure passwords, and build trust in our digital interactions. The next time you log into a website or see a checksum for a download, you’ll know there’s a powerful piece of mathematical magic working behind the scenes to keep your digital life safe.